Comprehensive Approaches to Personal Data Protection: Legal and Technical Perspectives

In the digital era, personal information and data have become essential for economic growth, innovation, public administration, and social development. While the use of personal data brings important commercial, economic, and social benefits, it remains crucial to protect individuals’ privacy and fundamental rights. If personal data is not handled properly, it can expose both individuals and organizations to serious risks. Therefore, the pursuit of economic value from personal data should never weaken the safeguards that protect privacy and fundamental rights.
Effective protection of personal data requires two key elements: strong regulatory frameworks and practical implementation measures. Regulatory frameworks establish clear legal rules that govern how personal data is collected, processed, stored, transferred, and shared. On the other hand, practical implementation measures focus on technical and operational solutions that protect data from breaches and unauthorized access. Together, these elements create a balanced system that promotes compliance, security, and accountability, ensuring that organizations both follow legal requirements and apply effective safeguards while managing personal data responsibly.
This report will examine the key aspects of personal data protection through two main dimensions: First, the legal dimension especially under the Jordanian Personal Data Protection Law No. 24 of 2023, which covers the principal legal mechanisms for personal data protection. Second, the technical dimension which covers the practical technical measures that organizations can implement to secure personal data against risks such as breaches and unauthorized access. Additionally, it will address the primary risks threatening data protection and the technical measures organizations can implement to mitigate these risks, providing a comprehensive view of how personal data can be effectively safeguarded.
Personal data has become one of the most valuable assets in the modern world. It plays a central role in economic development, business operations, public governance, and even in shaping social and political dynamics. With the rapid advancement of digital technologies, the volume of personal data collected, stored, and processed has increased significantly, making its protection more critical than ever.
This part of the report explains the importance of personal data from different perspectives as follows:
Personal data is now a key driver of the digital economy, especially in supporting modern economies. Today, the shift from a traditional economy, based on physical goods and conventional production, to a digital economy driven by technology and information is evident. Unlike the past, where natural resources, capital, and labor were the primary drivers of economic activity, the modern economy centers on digital services, platforms, and information-based products that are delivered and consumed online.
In this context, personal data has become a vital economic resource that supports service improvement, operational efficiency, consumer insight, demand forecasting, and strategic decision-making across sectors. The following points highlight its economic significance:
- Data as an economic asset: Nowadays personal data is often compared to “the new oil” referring to its strong economic value in the digital economy. In today’s economy, personal data is recognized as an important economic resource that contributes to overall growth, innovation, and efficiency across all sectors of society including public services, markets, and digital infrastructure.
- Innovation and technology growth: Sectors such as artificial intelligence (AI), cloud computing, and financial technology (FinTech) rely heavily on access to large amounts of accurate data. For example, In the financial technology sector, companies use big data analytics to help detect fraud by identifying unusual patterns in transactions, and to offer personalized financial products and services based on individual customer data.
- Employment and investment: The growth of the data economy support and increase the creation of jobs such as cybersecurity, data management, software development, and compliance, and also attracts both local and international investments by making the business environment more competitive and innovation.
The economic value of personal data continues to increase as more services move online and as the global economy becomes more data driven.
Like any other strategic business resource, personal data is not less important than other inputs that support businesses successes as it plays a significant and effective role in identify consumer needs and behaviors, forecast demand, and optimize their services. Businesses collect and use personal data to improve their operations and provide better services. Data collection become essential for their strengthening competitiveness and continuity. Key aspects include:
- Customer relationship management: Personal data helps companies understand customer behavior, purchasing habits, and preferences. By analyzing these data businesses will be able to offer targeted services and improve customer satisfaction.
- Decision making: Businesses rely on data to make strategic decisions, reduce risks, and increase efficiency.
Reputation and trust: Protecting customers personal data enhances the company’s reputation and builds long-term trust. On the other hand, data breaches can lead to financial losses and damage to the company’s public image and brand value.
The importance of personal data is not limited to the technological, economic, or commercial domains; it has extended to include essential roles in government services and political affairs, where data increasingly inform public administration and policy decisions. Governments use personal data to provide public services, maintain security, and support national development. Proper use of data can improve the effectiveness and fairness of public administration. Some key points include:
- Public service delivery: Personal data allows governments to deliver targeted and efficient services in health, education, social protection, and public administration. By understanding citizens’ needs through data, public programs can be tailored and resources better allocated.
- National security and law enforcement: Governmental authorities use personal data to detect and prevent illegal activities, fight cybercrime, and protect the community.
- Policy-making: Data helps decision makers understand social and economic trends and develop evidence-based policies.
However, the political use of data must always respect privacy rights and legal safeguards, ensuring that data is not misused or exploited for illegitimate purposes.
Personal data has a direct impact on individuals and their daily lives. Its proper protection strengthens confidence in digital services and supports a safe digital environment. The main social aspects include:
- Personal autonomy: Personal data represents parts of a person’s private life. Protecting it helps individuals maintain control over their identity and personal choices.
- Digital participation: Many essential services such as communication platforms, e-government applications, and online banking require sharing personal data. Ensuring its protection encourages people to use these services without fear.
Mismanagement or insufficient protection of personal data expose organizations and individuals to serious legal risks. These include:
- Non-compliance with laws: Most countries have data protection laws that require organizations and individuals to handle personal data responsibly and securely. Failure to comply with these legal obligations can result in fines, penalties, or legal action.
- Civil liability: Individuals (data subject) whose personal data has been misused, breached, or exposed may pursue civil claims for damages against the responsible organization or individual. In many legal systems, data subject has the right to seek compensation for harm resulting from unlawful processing or unauthorized access to their personal data.
- Contractual risks: Companies handling personal data for clients may breach contractual obligations if data is mishandled, leading to claims for damages.
- Reputational damage: Misuse or loss of personal data often come with public exposure -especially for organizations that have a wide reputation and provide world-class services- which will not only result to a legal risk but also long- term reputational damages, loss of stakeholder trust.
These legal risks highlight the importance of establishing strong internal policies, compliance mechanisms, and awareness programs to ensure that personal data is protected according to applicable laws.
Accordingly, personal data is important in economic, business, political, and social fields. Its value is increasing as digital transformation continues. For this reason, protecting personal data has become a priority for governments, companies, and individuals. Proper protection builds trust, supports development, and protects people’s rights.
This importance is the basis for the legal and technical frameworks for data protection, which will be explained in this report.
Given the significant value of personal data in the modern world, as explained in the first part of this report, the need for a clear, organized, and strict legal frame work for the protection of personal data has become urgent. For this purpose, the Hashemite Kingdom of Jordan recognized the importance of this subject and enacted legislation to regulate and protect personal data as a fundamental right of individuals. This legislation is the Personal Data Protection Law No. 24 of 2023 (referred to hereinafter as the “Law” or the “Jordanian Personal Data Protection Law” or “JPDPL”).
The Law regulates all matters related to personal data and sets out several legal rules to ensure the protection of personal data and prevent its unlawful use. This part of the report explains the main legal mechanisms for personal data protection under the Jordanian Personal Data Protection Law.
Before addressing these mechanisms, it is important to clarify some key terms for the reader as defined in the law:
- “Data Subject”: A natural person whose personal data is being processed.
- “Controller”: Any natural or legal person, whether inside or outside Jordan, who holds or controls personal data.
- “Processor”: The natural or legal person who is responsible for processing the data.
- “DPO”: The natural person designated to oversee databases and processing in accordance with the provisions of the Law.
Below are the most important legal safeguards established by the Jordanian Law to protect personal data:
The Law requires that no personal data may be processed without first obtaining the prior consent of the Data Subject. This prior consent has legal requirements, including:
- It must be clear and documented, either in writing or electronically. Verbal consent is not acceptable.
- It must specify the purpose and duration of the consent. The request must clearly state why the data is being collected and for how long the consent remains valid.
- It must be written in clear, simple, and non-misleading language, ensuring that individuals are not tricked due to unfamiliarity with legal or technical terms.
The Law imposes several restrictions and conditions on processing personal data, to ensure that collected data is not used unlawfully. The key restrictions include:
- Legitimate Purpose: The most important restriction imposed by law on data processing is that data may only be processed for purposes and this purpose must be specified, explicit, and lawful.
- Processing limitation: Processing must remain within the specific purpose for which the data was originally collected and consented to.
- Lawful and fair processing methods must be used.
- Confidentiality: Processing must ensure the confidentiality and security of personal data and prevent alteration, or unauthorized disclosure.
Data deletion: Personal data must be deleted once the processing period has expired.
The Law obliges controllers (natural or legal person holding personal data) to protect the data under its custody. Key responsibilities of the controller include:
- Take all the security, technical, and organizational measures to ensure the data confidentiality, safety, and protection against any unauthorized access, use, disclosure, destruction, modification.
- Establishing a suitable infrastructure and having a qualified team for data processing and for receiving and responding to complaints.
- Set clear procedures to allow data subjects to exercise their rights, including correcting their data, objecting the processing, withdrawing consent, accessing and updating their data in a secure and effective way.
These compliance functions may be handled internally or outsourced to a specialized external provider, depending on the size, capacity, and needs of the organization.
Like data protection laws in other countries, the Jordanian Law requires Controllers to appoint a Personal Data Protection Officer (DPO) to ensure compliance and protect the rights of Data Subjects. Key responsibilities of the DPO include:
- Monitoring and documenting the Controller’s compliance with the Law.
- Conducting regular assessments of data systems and issuing recommendations.
- Acting as the liaison with the Data Protection Directorate and with security and judicial authorities.
- Enabling Data Subjects to exercise their legal rights.
- Providing training programs for the Controller’s staff on data protection.
The Law classifies organizations with respect to the DPO requirement into three categories:
A. Entities Required to Appoint a DPO Without Prior Accreditation:
These entities must appoint a DPO without needing accreditation from the Personal Data Protection Council. They include:
- Entities whose main activity is processing personal data.
- Entities that process sensitive personal data.
- Entities processing data of persons lacking legal capacity.
- Entities processing financial data.
- Entities transferring databases outside Jordan.
B. Entities Required to Appoint a DPO With Prior Accreditation:
These entities must obtain accreditation from the Personal Data Protection Council before appointing the DPO, due to the sensitivity of the data they handle. They include:
- Telecommunications and information technology sector.
- Energy sector.
- Water sector.
- Health sector.
- Transport sector.
C. Entities Not Required to Appoint a DPO:
Entities that do not fall under categories (A) or (B) are not obligated to appoint a DPO. However, they may do so voluntarily.

The Law sets several restrictions on the transfer of personal data to protect the rights of data subjects and prevent personal data from becoming publicly available or commercially exploited. Key restrictions include:
- Obtaining the Data Subjects’ consent before transferring their personal data.
- Ensuring that the transfer serves legitimate interests of both the Controller and the receiving party.
- Informing the Data Subject of the identity of the recipient.
- Informing the Data Subject of the purpose of the transfer.
- Prohibiting the use of transferred data for marketing purposes unless the Data Subject consents.
- For transfers outside Jordan, the receiving country must provide a level of data protection not less than that required under Jordanian law.
In the event of any breach or incident that may compromise the security of personal data, the Controller must:
- Notify affected Data Subjects within 24 hours of discovering the breach.
- Notify the Personal Data Protection Directorate within 72 hours of discovering the breach.
The Jordanian Personal Data Protection Law not only safeguards individuals’ personal data and prevents its misuse, but also shields organizations that handle such data from potential legal violations.
To implement these protections effectively, organizations need a team combining legal knowledge and technical expertise: legal proficiency ensures compliance with the law and protection of rights, while technical capability guarantees secure and proper data management. This combination turns legal obligations into practical actions, strengthens trust, and minimizes risks for both individuals and organizations.
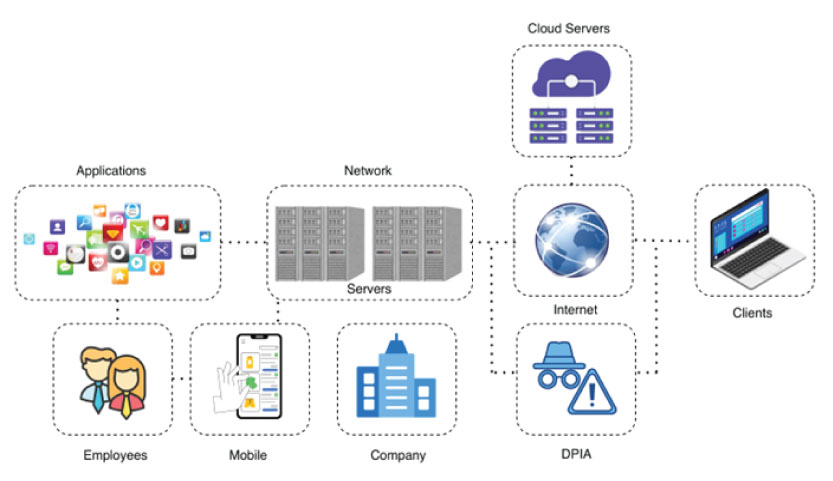
The diagram below, shows a high-level view of a modern company’s digital ecosystem. It illustrates the interconnected landscape where sensitive data lives and moves, highlighting the critical domains that require robust protection:
- Core Infrastructure: Data resides on Cloud Servers and internal Servers, and is accessed through corporate Applications.
- Access Points: Employees connect via Company networks, and data flows over the public Internet to Clients and Mobile devices.
- Human Element: Ultimately, Employees interact with data across all these touch points.
Each component in this chain represents a potential vulnerability. A weakness in any single domain, whether a misconfigured cloud server, an unsecured application, or a compromised employee device, can lead to a devastating data breach.
This is where a Data Protection Impact Assessment (DPIA) becomes not just a compliance exercise, but a strategic necessity.
The following sections details the most critical cybersecurity vulnerabilities confronting modern organizations today, and how you can avoid such threats.
In the intricate digital ecosystem outlined, every access point—from cloud servers and internal applications to employee mobile devices—is guarded by a fundamental layer of security: authentication. At the heart of this layer lies the most ubiquitous yet vulnerable secret: the password.
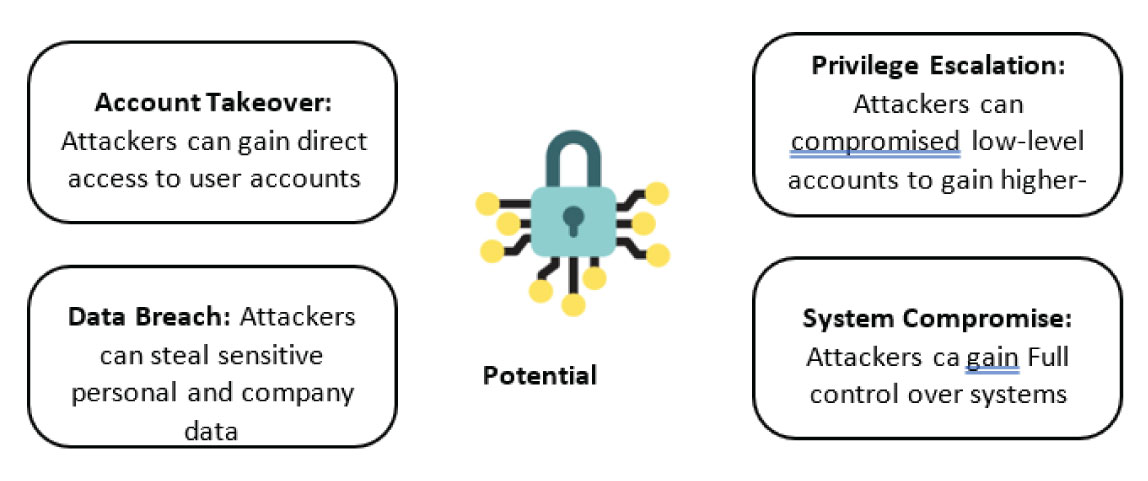
Despite advancements in biometrics and security keys, the password remains the primary key granting access to corporate data, email accounts, and critical systems. Consequently, it is also the most targeted element by cyber adversaries. Password attacks are not a new threat, but they have evolved in scale, sophistication, and automation, making them a persistent and devastatingly effective attack vector.
This section will dissect the most common and dangerous password attack methods threatening organizations today.
- What it is: Attackers send deceptive emails, texts, or instant messages that appear to be from a legitimate source (like IT, HR, or a well-known service like Microsoft).
- How it works: The message creates a sense of urgency (“Your password will expire!”) or curiosity (“You have a shared document”). It contains a link to a fake login page that looks identical to the real one. When an employee enters their credentials, they are sent directly to the attacker.
- Why it’s effective: It exploits human psychology and trust, bypassing technical controls entirely.

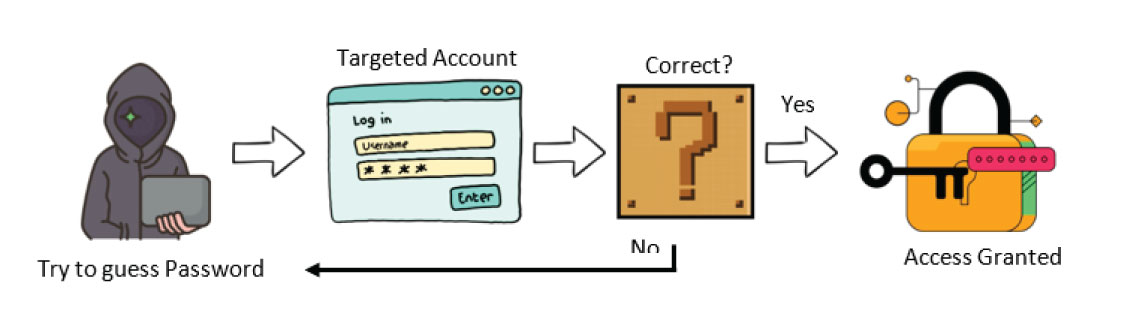
In the digital world, passwords act as locks. A brute force attack is the simplest way to break in: an attacker uses automated tools to try every possible password combination until they guess the correct one.
- What it is: Using automated software to guess a password by trying every possible combination of characters.
- How it works: The attacker systematically tries “password1”, “password2”, etc., or uses powerful computers to cycle through complex combinations. This is most effective against short, simple passwords.
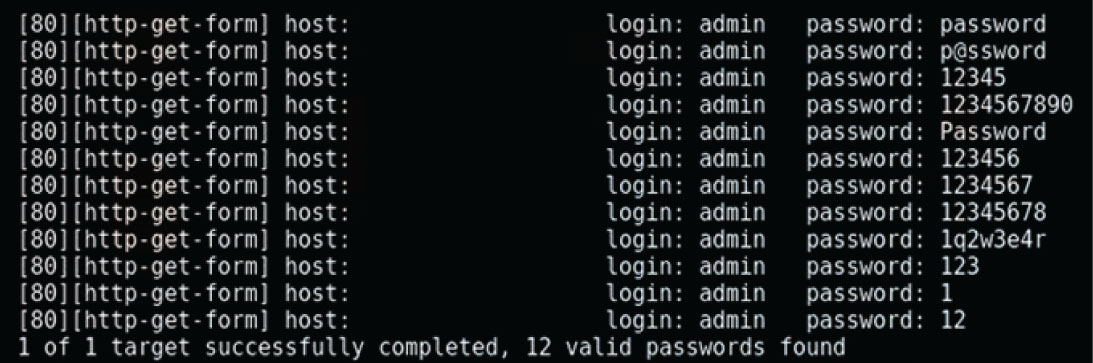
Why it’s effective: It is guaranteed to eventually guess the password; the only variable is time. Weak passwords can be cracked in seconds, as shown in the following example:
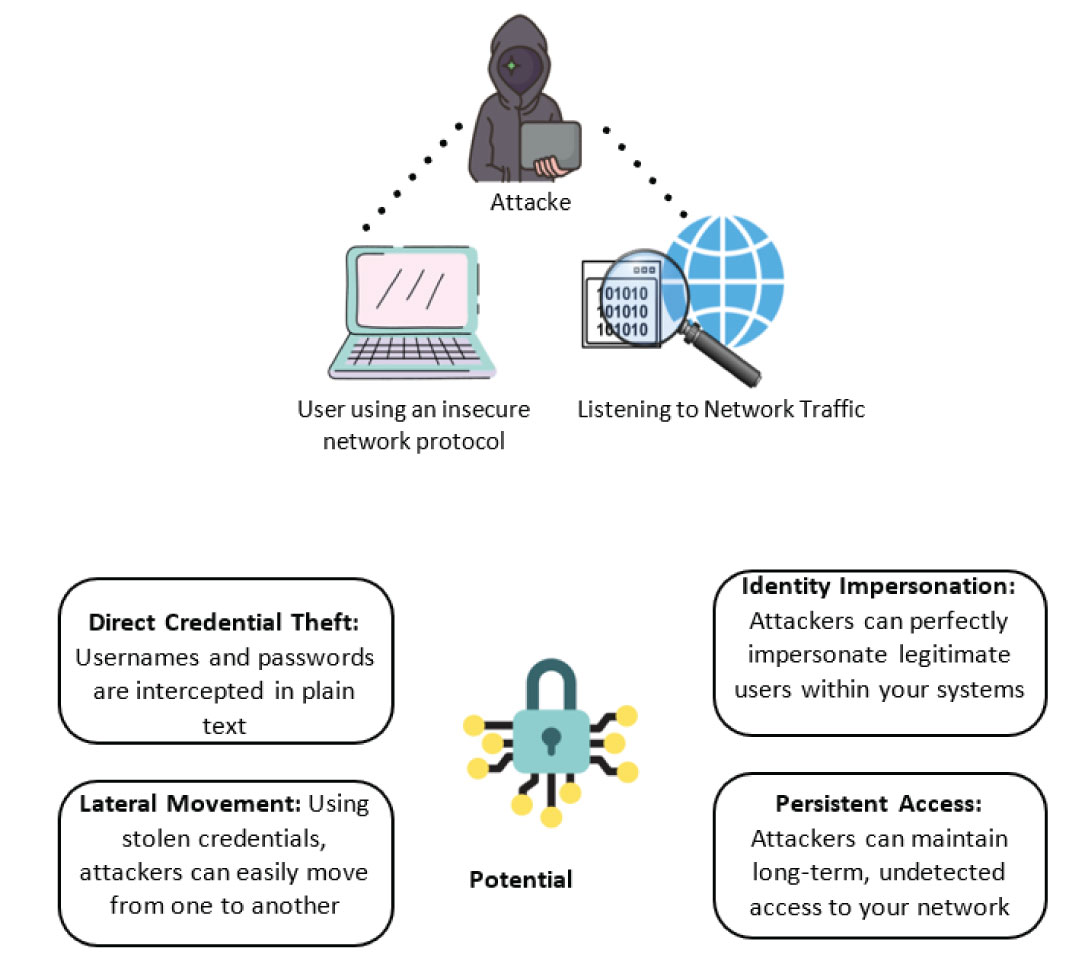
While many attacks focus on guessing or phishing passwords, a more passive and insidious method involves simply “listening” for them as they travel across the network.
What it is: Network Sniffing & Cleartext Transmission
This attack involves using software, to capture and inspect all data packets flowing across a network. If the data is not encrypted, the attacker can read it directly, much like eavesdropping on a conversation.
The critical vulnerability here is the use of cleartext (or plaintext) protocols. These are legacy methods of communication that do not encrypt the information they send.
- How it Works:
If a user or system uses one of these insecure protocols to log in, their username and password are captured in a readable format by the attacker.
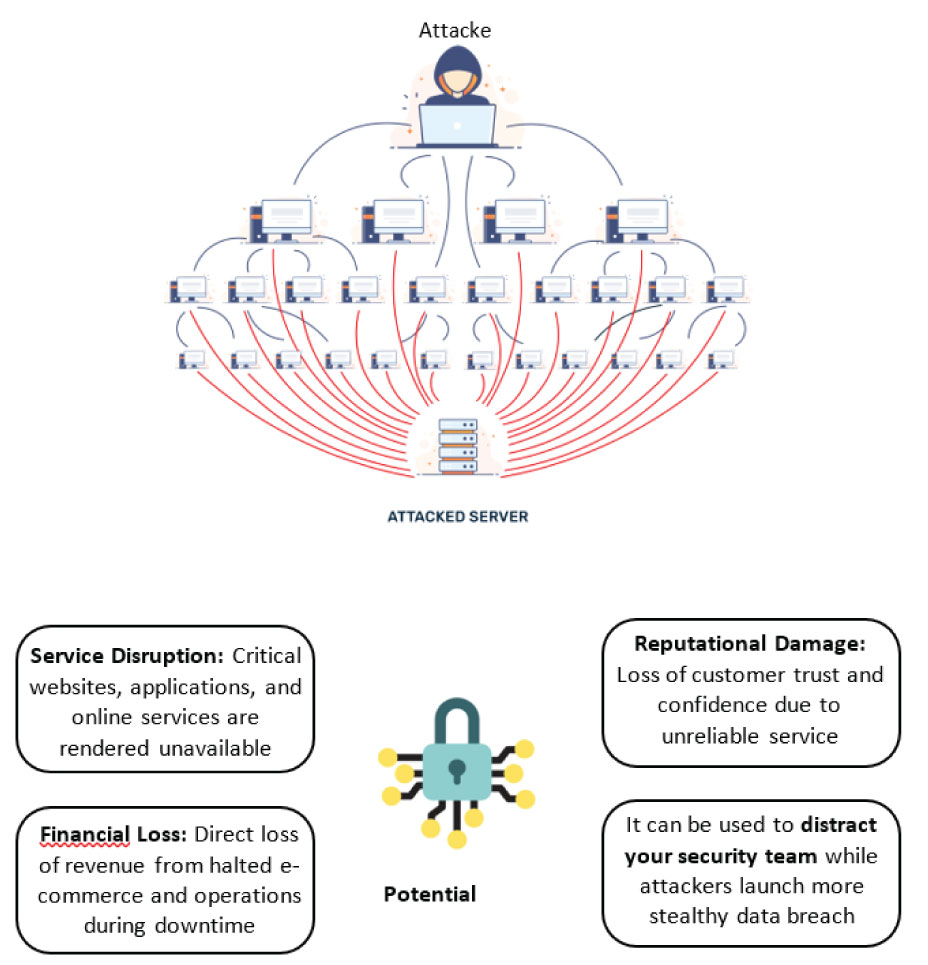
A Denial-of-Service (DoS) attack is not an attempt to steal data, but to make it unavailable. The objective is to overwhelm a company’s server, website, or network with a flood of illegitimate traffic—so much traffic that it cannot respond to legitimate requests from real users or customers.
Think of it like phoning a restaurant thousands of times a minute. The phone lines become jammed, and legitimate customers cannot get through to place an order.
A Distributed Denial-of-Service (DDoS) attack is a larger-scale version, where the attack originates from thousands of compromised devices simultaneously, making it much harder to block.
Impact: This results in website downtime, disrupted services, massive financial losses from halted e-commerce, and severe damage to brand reputation and customer trust.
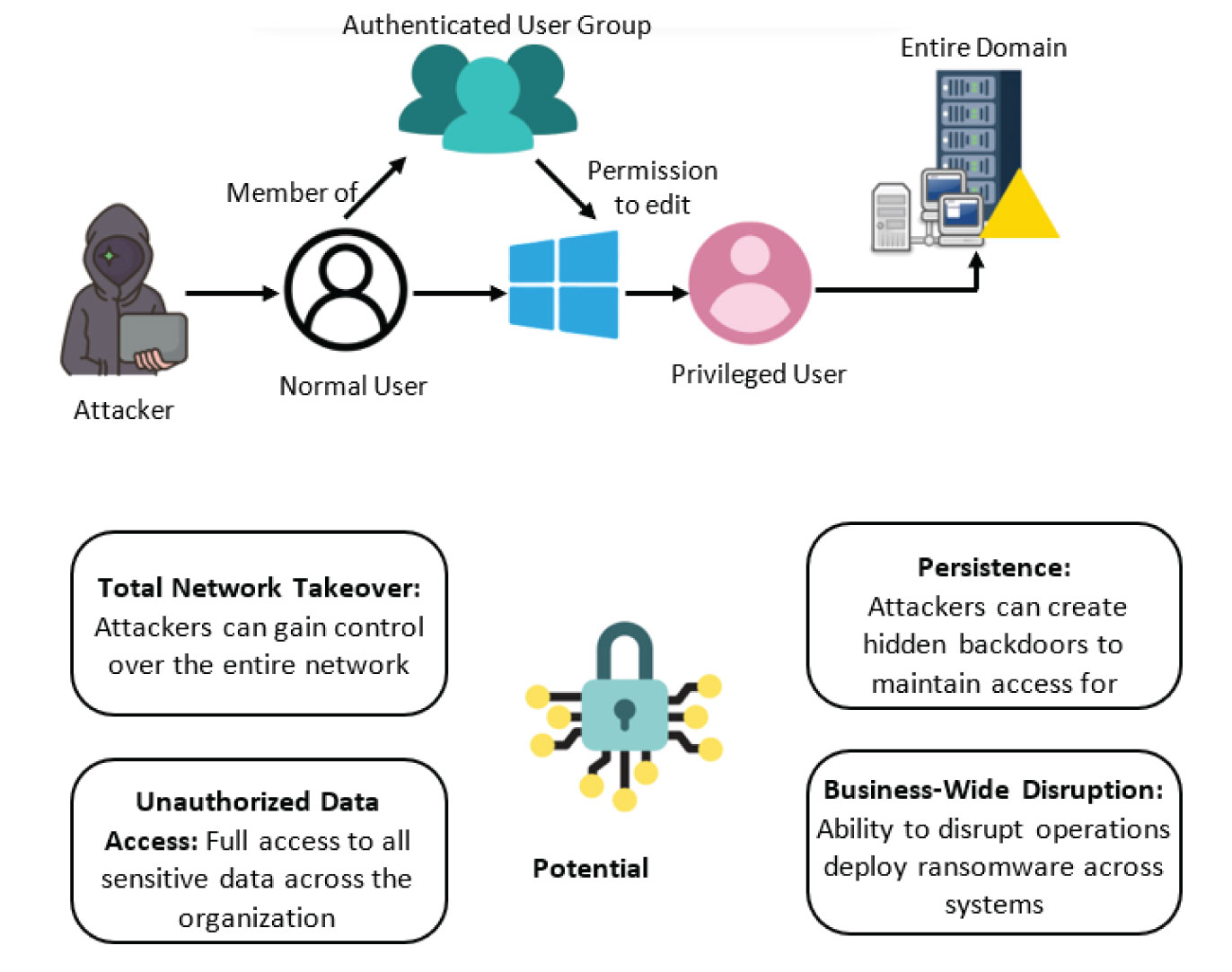
Active Directory (AD) is the central authentication and authorization system for most Windows-based corporate networks. It is the “digital phonebook” that manages every user, computer, and permission. Because of its central role, AD is the ultimate prize for cyber attackers.
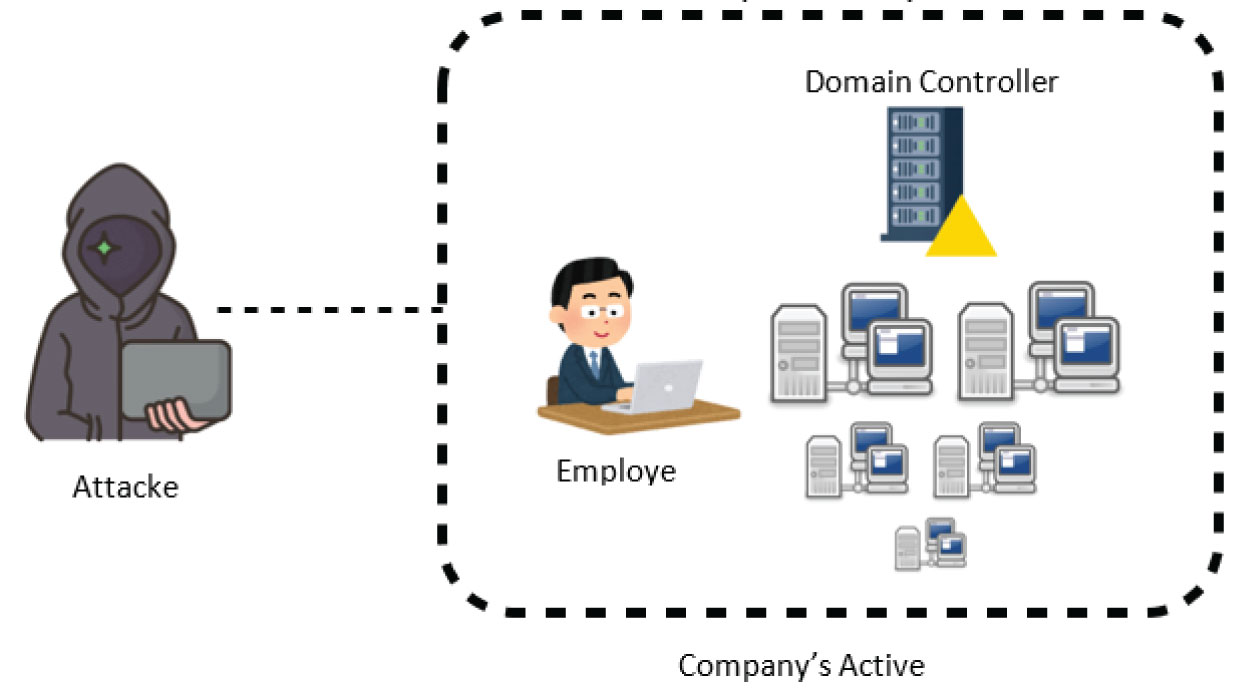
An Active Directory attack is not a single technique but a multi-stage campaign where attackers, after gaining an initial foothold, methodically move to compromise the core AD infrastructure itself. Their objective is to escalate privileges and ultimately gain control over the highest-level administrative accounts.
Once this control is achieved, they possess total, often undetectable, authority over the entire AD Domain. This allows them to access or exfiltrate any data, move laterally at will, and deploy persistent threats across all connected systems, making remediation incredibly complex and costly.
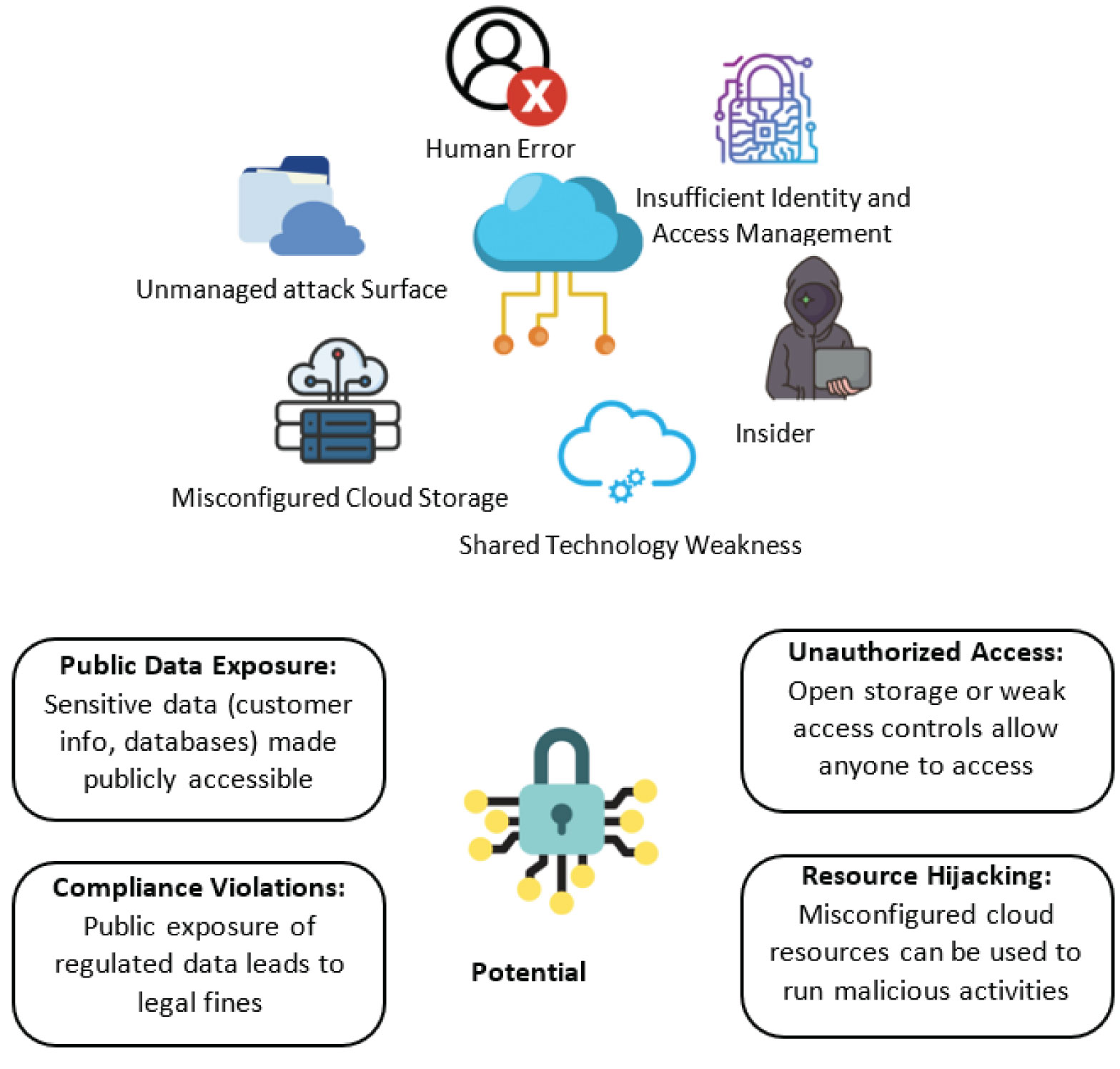
Cloud misconfiguration occurs when cloud services are set up with incorrect security settings, inadvertently exposing them to the public internet.
Unlike a sophisticated breach, this is often the result of human error, complex interfaces, or a misunderstanding of the “shared responsibility model” in the cloud. The result is a wide-open digital door, leaving sensitive data—including customer records, intellectual property, and internal communications—accessible to anyone who knows where to look, without the need to hack in.
- Human Error: The Unintentional Insider
The biggest risk is often a simple accident by an employee. This could be sending an email to the wrong person, clicking a bad link, or accidentally changing a setting that makes data visible to the public.
- Insufficient Identity and Access Management (IAM)
This means not managing who can see what inside your company’s cloud. Problems include using weak passwords, not having extra login steps, and giving employees access to data they don’t actually need for their job. This makes it easy for hackers to get in.
- The Insider Threat: A Breach from Within
Sometimes, the problem comes from a current or former employee. They might intentionally steal information, or they might accidentally cause a leak by being careless.
- Shared Responsibility Model Confusion
In the cloud, security is a team effort between your company and the cloud provider. Often, companies get confused and think the provider is handling everything, when in reality, they are responsible for protecting their own data and user accounts. This misunderstanding leaves major gaps.
- Misconfigured Cloud Storage
A very common cause of cloud data leaks is simple misconfiguration. It’s like accidentally storing your company’s private documents in a public, unlocked parking lot instead of a secure filing cabinet. Anyone can find and take them.
- Unmanaged and Expanding Attack Surface
The cloud makes it easy to create new services and storage with a click. Without careful tracking, a company can quickly lose sight of everything it owns in the cloud, what data is there, and who can access it. You can’t protect what you don’t know you have.
What it is: Web attacks are when hackers find and exploit weaknesses in your company’s website or web applications.
How it exposes sensitive data: These vulnerabilities act like unlocked doors or weak spots in your digital storefront. Hackers can use techniques like:
- Injecting malicious code to trick your website into revealing customer information
- Intercepting unsecured data transmissions
- Bypassing login systems to access protected areas
When successful, these attacks can expose:
- Customer credit card information (Visa/Mastercard numbers)
- Personal identification data
- Login credentials
- Private business documents
The consequence: A single web vulnerability can lead to massive data breaches, financial losses, and permanent damage to your company’s reputation.
- What it is: An attack where a hacker “tricks” your website into revealing the contents of its database.
- How it works: Imagine your website’s database is a secure vault that holds all customer information. When a user types a name into a search box, your website asks the vault: “Show me the profile for [Name]”.
A hacker will type a malicious command instead of a name. If your website isn’t properly secured, it will pass this command directly to the database vault, which will obediently execute it. The command could be: “Show me EVERY user’s credit card number and password.” - Why it’s dangerous: It can directly expose your entire database of customer records, including credit card information, personal details, and login credentials, as shown:

What Is a Third-Party Attack?
A third-party attack happens when hackers target your company by breaking into one of your vendors, suppliers, or partners. Imagine you have a highly secure office building, but the cleaning company you hire leaves a back door unlocked.
A thief uses that unlocked door to get into your office and steal your secrets. That’s exactly how third-party attacks work.
How Do Attackers Exploit This?
Attackers look for the weakest link in your business relationships. Instead of attacking your well-protected systems directly, they target your less-secure partners who have special access to your data or systems. For example:
- They might hack a software provider that manages your customer database.
- They could breach a cloud storage vendor where you keep sensitive files.
- They might breach a payment processing company, stealing credit card information from all the businesses that used its services.

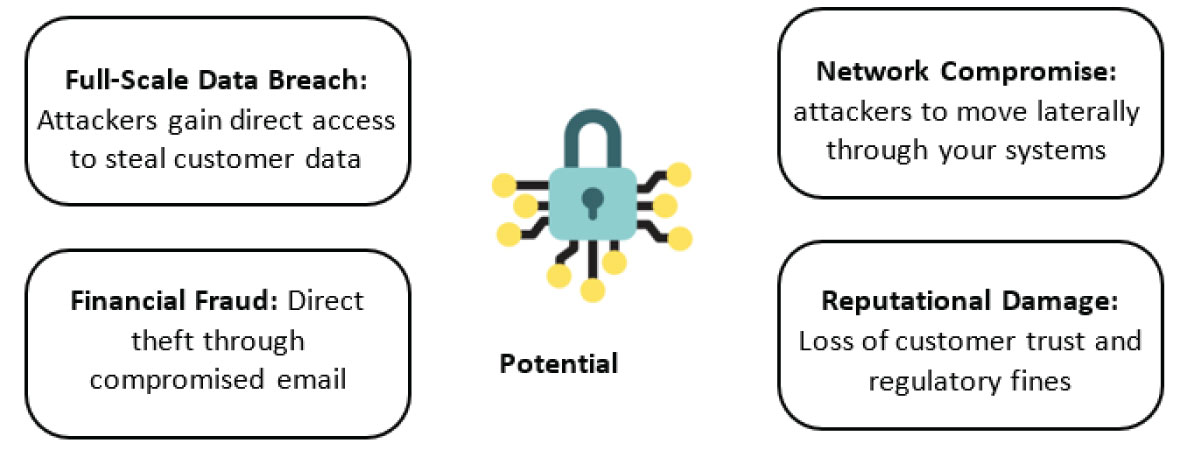
The modern threat landscape demonstrates that vulnerabilities could exist at every layer of an organization. No single tool can provide complete protection.
A strategic and integrated solution can be adopted to address the increasing complexity of cyber threats by moving beyond fragmented defensive measures toward a comprehensive framework that embeds security and privacy within organizational operations. Under this approach, regulatory compliance becomes a natural outcome of a well-structured and secure operational environment.
This solution is based on the following pillars:
- A strategic, holistic framework: The adoption of a unified strategy designed to protect the organization’s entire digital ecosystem through coordinated technical, organizational, and legal measures, supported by continuous risk assessment and management.
- Proactive compliance and defense: The implementation of preventive technical safeguards supported by comprehensive Data Protection Impact Assessments (DPIAs) to systematically identify, evaluate, and mitigate potential risks to personal data.
- Development of a security culture: The establishment of tailored internal security and data protection policies, combined with ongoing employee awareness and training programs to promote consistent compliance and responsible data handling practices.
- Integrated PDPL compliance: Ensuring full compliance with applicable Personal Data Protection Law (PDPL) requirements while positioning data protection as a strategic organizational asset rather than merely a regulatory obligation.

| Term | Definition |
| Authentication | is proving you are who you claim to be before being granted access. |
| Authorization | is what you're allowed to do and see after you've proven your identity. |
| Encryption | means your information is scrambled into a secret code that only someone with the right key can unlock and read. |
| Network | is a digital highway that connects computers and devices, allowing them to share information and resources. |
| Network Traffic | is all the information—messages, videos, files—that travels between devices on a network. |
| Network Protocol | is a set of rules that devices follow to communicate, just like the rules of the road (stop signs, traffic lights) that ensure cars can drive safely and orderly. |
| Corporate Network | is a private, internal highway system that connects all of a company's computers, phones, and servers, allowing employees to securely share information and resources within the organization. |
| Initial Foothold | is the first point of access a hacker manages to get inside a company's network. |
| Escalating privileges | is when a hacker who has a low-level access pass finds a way to get a master key, giving them full control over the entire system. |
| Active Directory Domain | is the central security hub for a Windows-based company network. It acts as a master directory that manages every user, computer, and their access permissions, ensuring the right people can access the right resources. |
| Exfiltrate Data | means to secretly steal and copy information from a company's network and send it to an outside location controlled by the attacker. |
| Moving Laterally | is when a hacker who has broken into one computer explores the network to find and break into other, more important computers. |
| Database | is a highly organized digital filing cabinet where a company stores all its structured information, like customer details, product lists, and financial records, so it can be easily found, managed, and updated. |
| Potential Vulnerability | is a weakness or a flaw in a system—like an unlocked door or a broken window—that a hacker could potentially find and exploit to break in. |
| Data Breach | is a security incident where sensitive or confidential information is stolen, copied, viewed, or used by someone who is not authorized to do so. |
| Data Protection Impact Assessment (DPIA) | is a formal process to identify and reduce the privacy risks of a new project before it starts, ensuring personal data is protected from the very beginning. |
| Exploitation | is the act of a hacker actively taking advantage of a specific weakness or vulnerability in a system to gain unauthorized access, steal data, or cause damage. |
| Shared Responsibility Model | The cloud provider secures the platform (like the building), while you secure your data and access (like your office inside). Both are responsible for different parts of security. |
Ma'in Nsair (Data protection specialist)
Tariq Aldiri (Data protection specialist)
Dina Al- Qawaqzeh (Cyber Security Specialist)
For more information, Please contact us at: info@nsairs.com
